age in a descending order of addresses, and both the
count and the address are stepped down. When the
count in any operation reaches zero, the storage area
defined by the ccw is exhausted.
Any main-storage location provided in the system
can be used to transfer data to or from anI/O device,
provided that during an input operation the location
is not protected. Similarly, the ccw's can be specified
in any part of available main storage. When the chan
nel attempts to store data at a protected location, the
protection-check condition is generated, and the de
vice is signaled to terminate the operation.
When the channel refers to a location not provided
in the system, the program-check condition is gener
ated. When this condition occurs because the first ccw
designated by the CAW contains a data address ex
ceeding the addressing capacity of the model, theI/O operation is not initiated, and the status portion of the
csw with the program-check indication is stored dur
ing execution ofSTART I/O. Invalid data addresses de
tected after initiation of the opcration or detection of
an invalid ccw address during chaining is indicated
to the program with the interruption conditions at the
termination of the operation or chain of operations.
During an output operation, thc channel may fetch
data from main storage ahead of the time theI/O de
vice requests the data. As many as 16 bytes may be
prefetehed and buffered. Similarly, on data chaining
during an output operation, the channel may fetch the
new ccw when as many as 16 bytes remain to be
transferred under the control of the current ccw.
When theI/O operation uses data and ccw's from 10- ations near the end of the available storage, such pre
fetching may cause the channel to refer to locations
that do not exist. Invalid addresses detected during
prefetching of data or ccw's do not affect the execu
tion of the operation and do not cause error indica
tions until theI/O operation actually attempts to use
the information. If the operation is terminated by theI/O device or by HALT I/O before the invalid informa
tion is needed, the condition is not brought to the
attention of the program.Storage addresses do not wrap around to location 0 unless the system has the maximum addressable stor
age (16,777,216 bytes). When the maximum address
able storage is provided, location0 follows location
16,777,215 and, on reading backward, location
16,777,215 follows locationO. The count field in the ccw can specify any number
of bytes up to 65,535. Except for a ccw specifying
transfer in channel, it may not contain the value zero.
Whenever the count field in the ccw initially contains
a zero, the program-check condition is generated.
When this occurs in the first ccw designated by the
98
CAW, the operation is not initiated, and the status por
tion of the csw with the program-check indication is
stored during execution ofSTART I/O. When a count
of zero is detected during data chaining, theI/O de
vice is signaled to terminate the operation. Detection
of a count of zero during command chaining sup
presses initiation of the new operation and generates
an interruption condition.Chaining When the channel has performed the transfer of in
formation specified by a ccw, it can continue the ac
tivity initiated bySTART I/O by fetching a new ccw.
The fetching of a new ccw upon the exhaustion of the
current ccw is called chaining and the ccw's belonging
to such a sequence are said to be chained.
Chaining takes place only between ccw's located
in successive double-word locations in storage. It pro
ceeds in an ascending order of addresses; that is, the
address of the new ccw is obtained by adding eight
to the address of the current ccw. Two chains of
ccw's located in noncontiguous storage areas can be
coupled for chaining purposes by a transfer in chan
nel command. All ccw's in a chain apply to theI/O device specified in the original START I/O. Two types of chaining are provided: chaining of
data and chaining of commands. Chaining is con
trolled by the chain-data (CD) and chain-command
(cc) flags in the ccw. These flags specify the action
to be taken by the channel upon the exhaustion of
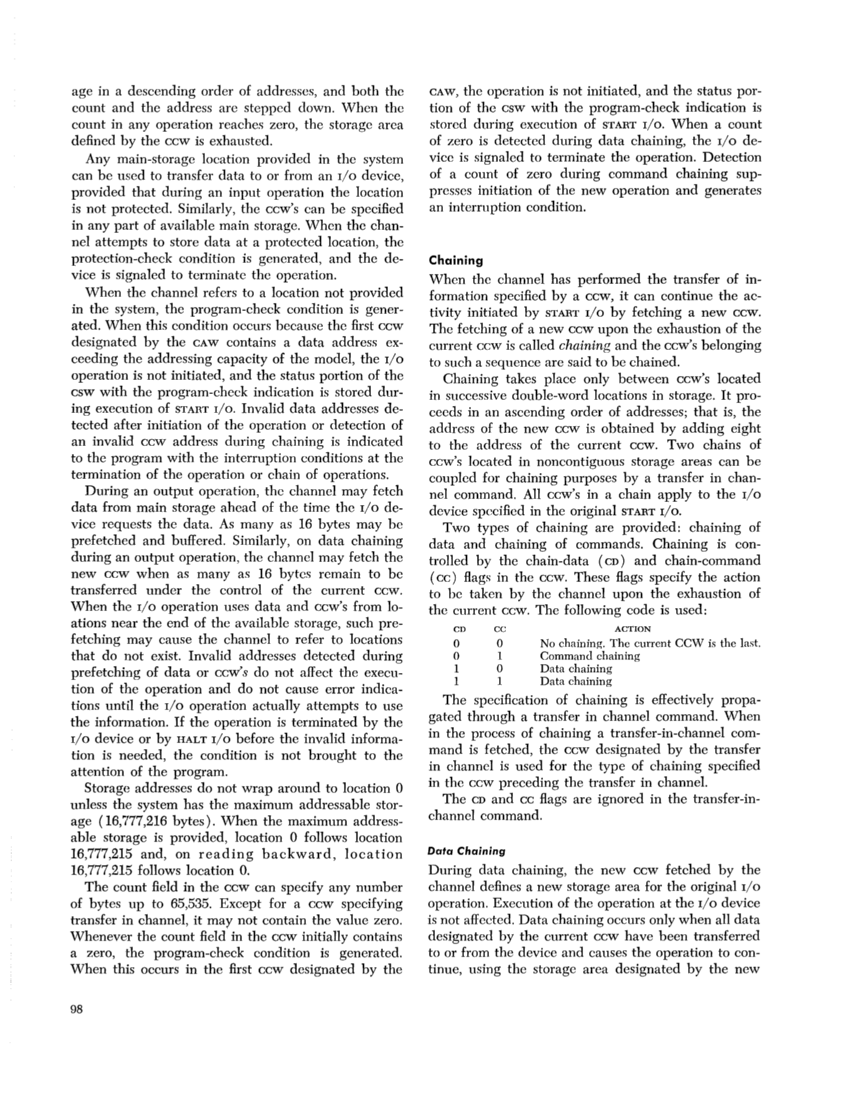
the current ccw. The following code is used:
CD CCACTION o 0 No chaining. The current CCW is the last.
o 1 Command chaining
10 Data chaining
1 1 Data chaining
The specification of chaining is effectively propa
gated through a transfer in channel command. When
in the process of chaining a transfer-in-channel com
mand is fetched, the ccw designated by the transfer
in channel is used for the type of chaining specified
in the ccw preceding the transfer in channel.
The CD and cc flags are ignored in the transfer-in
channel command.
Data Chaining
During data chaining, the new ccw fetched by the
channel defines a new storage area for the originalI/O operation. Execution of the operation at the I/O device
is not affected. Data chaining occurs only when all data
designated by the current ccw have been transferred
to or from the device and causes the operation to con
tinue, using the storage area designated by the new
count and the address are stepped down. When the
count in any operation reaches zero, the storage area
defined by the ccw is exhausted.
Any main-storage location provided in the system
can be used to transfer data to or from an
provided that during an input operation the location
is not protected. Similarly, the ccw's can be specified
in any part of available main storage. When the chan
nel attempts to store data at a protected location, the
protection-check condition is generated, and the de
vice is signaled to terminate the operation.
When the channel refers to a location not provided
in the system, the program-check condition is gener
ated. When this condition occurs because the first ccw
designated by the CAW contains a data address ex
ceeding the addressing capacity of the model, the
csw with the program-check indication is stored dur
ing execution of
tected after initiation of the opcration or detection of
an invalid ccw address during chaining is indicated
to the program with the interruption conditions at the
termination of the operation or chain of operations.
During an output operation, thc channel may fetch
data from main storage ahead of the time the
vice requests the data. As many as 16 bytes may be
prefetehed and buffered. Similarly, on data chaining
during an output operation, the channel may fetch the
new ccw when as many as 16 bytes remain to be
transferred under the control of the current ccw.
When the
fetching may cause the channel to refer to locations
that do not exist. Invalid addresses detected during
prefetching of data or ccw's do not affect the execu
tion of the operation and do not cause error indica
tions until the
the information. If the operation is terminated by the
tion is needed, the condition is not brought to the
attention of the program.
age (16,777,216 bytes). When the maximum address
able storage is provided, location
16,777,215 and, on reading backward, location
16,777,215 follows location
of bytes up to 65,535. Except for a ccw specifying
transfer in channel, it may not contain the value zero.
Whenever the count field in the ccw initially contains
a zero, the program-check condition is generated.
When this occurs in the first ccw designated by the
98
CAW, the operation is not initiated, and the status por
tion of the csw with the program-check indication is
stored during execution of
of zero is detected during data chaining, the
vice is signaled to terminate the operation. Detection
of a count of zero during command chaining sup
presses initiation of the new operation and generates
an interruption condition.
formation specified by a ccw, it can continue the ac
tivity initiated by
The fetching of a new ccw upon the exhaustion of the
current ccw is called chaining and the ccw's belonging
to such a sequence are said to be chained.
Chaining takes place only between ccw's located
in successive double-word locations in storage. It pro
ceeds in an ascending order of addresses; that is, the
address of the new ccw is obtained by adding eight
to the address of the current ccw. Two chains of
ccw's located in noncontiguous storage areas can be
coupled for chaining purposes by a transfer in chan
nel command. All ccw's in a chain apply to the
data and chaining of commands. Chaining is con
trolled by the chain-data (CD) and chain-command
(cc) flags in the ccw. These flags specify the action
to be taken by the channel upon the exhaustion of
the current ccw. The following code is used:
CD CC
o 1 Command chaining
1
1 1 Data chaining
The specification of chaining is effectively propa
gated through a transfer in channel command. When
in the process of chaining a transfer-in-channel com
mand is fetched, the ccw designated by the transfer
in channel is used for the type of chaining specified
in the ccw preceding the transfer in channel.
The CD and cc flags are ignored in the transfer-in
channel command.
Data Chaining
During data chaining, the new ccw fetched by the
channel defines a new storage area for the original
is not affected. Data chaining occurs only when all data
designated by the current ccw have been transferred
to or from the device and causes the operation to con
tinue, using the storage area designated by the new