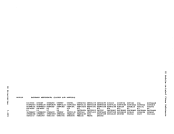
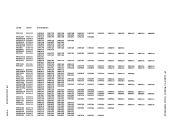
INITIALIZATION AND TERMINATION
AfterCP has been initialized, DMKCPVEN enables the communication lines
in response to the ENABLE command. Then an individual virtual machine
is attached to the system, using the following steps:
1.!~rmi~g1_Ident!!!£at!~~ When the CP receives the initial interrupt from a terminal on an
enabled line (normally initiated by a user dialing inOn a
data-set), theDMKCNSIN routine is entered. DMKCNSIN determines
the terminal device type, stores this information in the terminaldevice bleck, writes the online message and puts the terminal line
in a state to receive an attention interruption.
After the online message has been displayed at the user's terminal,
and he has pressed the ATTENTION key,DMKCNSIN (the console
interruption routine) callsDKKBLDV8 to build a skeleton VMBLOK for
the user. At this time, the userid isLOGONxxx, where xxx is the
terminal real device address, and a flag is set to indicate that
the user has not yet completed the logon process.
ThenDMKCNSIN calls DMKCFMBK~ which types a single blank at the
terminal, and issues a read to the terminal for the user to enter
his firstcommand (normally LOGON or DIAL).
After the first command has been entered by the user,DMKCNSIN further determines the type of terminal. If the terminal is a
2741,DMKTRMID is called to identify it as either a 2741P
(PTTC/EBCD) or a 2741C (Correspondence) terminal. If successful,
the correct device type and translate tables for input and output
are set; iffiot, flags are set to indicate that the terminal is
not yet identified.
Then control is returned toDMKCFMBK, which determines if the first
command is valid (for example,LOGON, ftSG, or DIAL). If the first
command is not valid, a restart message is given, and the read to
the terminal occurs again for the first command. If the first
command wasLOGON (or its abbreviation), DMKLOGON is called to
complete the process of attaching the virtualmachine to the
system.
The operations performed byDMKLOGON include the following: • Ensures that the maximum number of virtual machines allowed on
the system is not being exceeded.• Obtains the userid from the command line, and chects for a
possible password and other optional operands.• Checks the userid and password (entered separately if not on the LOGON command line) against entries in CP's directory of users. CP Introduction 1-123
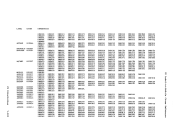
After
in response to the ENABLE command. Then an individual virtual machine
is attached to the system, using the following steps:
1.
enabled line (normally initiated by a user dialing in
data-set), the
the terminal device type, stores this information in the terminal
in a state to receive an attention interruption.
After the online message has been displayed at the user's terminal,
and he has pressed the ATTENTION key,
interruption routine) calls
the user. At this time, the userid is
terminal real device address, and a flag is set to indicate that
the user has not yet completed the logon process.
Then
terminal, and issues a read to the terminal for the user to enter
his first
After the first command has been entered by the user,
2741,
(PTTC/EBCD) or a 2741C (Correspondence) terminal. If successful,
the correct device type and translate tables for input and output
are set; if
not yet identified.
Then control is returned to
command is valid (for example,
command is not valid, a restart message is given, and the read to
the terminal occurs again for the first command. If the first
command was
complete the process of attaching the virtual
system.
The operations performed by
the system is not being exceeded.
possible password and other optional operands.