a subsequent fetch may find an invalid CBC. When TEST BLOCK is installed, it will,
in most cases, be the most effective
instruction in validating storage. When
TESTBLOCK is not installed, MOVE LONG, depending on the model, may prove effec
tive.
The effectiveness of the following
guideline depends on the model.On some
models, instructions may be implemented
that are more effective than the one
listed here; however, the following
approach is recommended when a model
dependent routine cannot be justified.
Execution ofMOVE LONG will be most
effective in validating the main-storage
area containing the first operand when
the following conditions are satisfied:• The first-operand field and
second-operand field participating
in the operation do not overlap.• The first-operand field starts on a
2K-byte boundary and is 2K bytes
(or a multiple of 2K bytes)in length. • The second-operand field, if nonze
ro in length, starts on a 2K-byte
boundary and is 2K bytes (or a
multiple of 2K bytes) in length.• In general, the validation will be
more effective if the second
operand field is of zero length. A
nonzero-length second operand
should be specified only if it is
required to restore the contents of
the block without introducing
intermediate values.
An interruption
during execution
affect the
performed.
or stopping of
ofMOVE LONG validation
INVALIDCBC IN STORAGE KEYS
theCPU does not
function
Depending on the model, each storage key
may be contained in a single checking
block, or the access-control and fetch
protection bits and the reference and
change bits may be in separate checking
blocks.
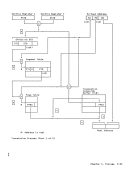
The figure "InvalidCBC in Storage Keys"
describes the action taken when the
storage key has invalidCBC. The figure
indicates the action taken for the case
when the access-control and fetch
protection bits are in one checking
block and the reference and change bits
are ina separate checking block. In
machines where both fields are included
in a single checking block, the action
taken is the combination of the actions
for each field in error, except that
completion is permitted only if an error
in all affected fields permits
completion. References to main storage
to which key-controlled protection does
not apply are treated as ifan access
key of zero is used for the reference.
This includes such references as
channel-program references during
initial program loading and implicit
references, such as interruption action
and OAT-table accesses.Chapter 11. Machine-Check Handling 11-7
in most cases, be the most effective
instruction in validating storage. When
TEST
tive.
The effectiveness of the following
guideline depends on the model.
models, instructions may be implemented
that are more effective than the one
listed here; however, the following
approach is recommended when a model
dependent routine cannot be justified.
Execution of
effective in validating the main-storage
area containing the first operand when
the following conditions are satisfied:
second-operand field participating
in the operation do not overlap.
2K-byte boundary and is 2K bytes
(or a multiple of 2K bytes)
ro in length, starts on a 2K-byte
boundary and is 2K bytes (or a
multiple of 2K bytes) in length.
more effective if the second
operand field is of zero length. A
nonzero-length second operand
should be specified only if it is
required to restore the contents of
the block without introducing
intermediate values.
An interruption
during execution
affect the
performed.
or stopping of
of
INVALID
the
function
Depending on the model, each storage key
may be contained in a single checking
block, or the access-control and fetch
protection bits and the reference and
change bits may be in separate checking
blocks.
The figure "Invalid
describes the action taken when the
storage key has invalid
indicates the action taken for the case
when the access-control and fetch
protection bits are in one checking
block and the reference and change bits
are in
machines where both fields are included
in a single checking block, the action
taken is the combination of the actions
for each field in error, except that
completion is permitted only if an error
in all affected fields permits
completion. References to main storage
to which key-controlled protection does
not apply are treated as if
key of zero is used for the reference.
This includes such references as
channel-program references during
initial program loading and implicit
references, such as interruption action
and OAT-table accesses.